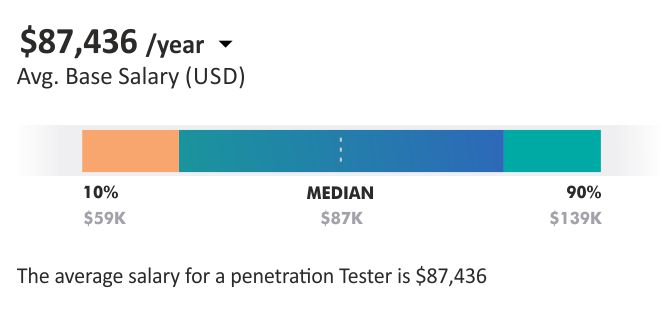
Certified Penetration Testing Professional (CPENT)
The Certified Penetration Testing Professional or CPENT re-writes the standards of penetration testing skill development. EC-Council CPENT program educates participants on how to achieve an application penetration test in an enterprise network environment. The penetration includes attack, exploit, evade, and defense.
- 40 Hours Instructor led Online Training
- Authorized Digital Learning Materials
- Lifetime Free Content Access
- Flexible Schedule Learn Anytime, Anywhere.
- Training Completion Certificate
- 24x7 After Course Support
Accreditation with