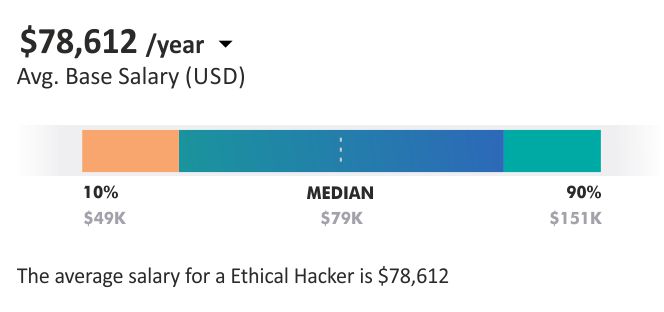
Certified Ethical Hacker (CEH v12)
EC-Council’s Certified Ethical Hacker (CEH v12) trains the students to hack a network under the guidance of the law. In CEH training, participants get equipped with the trending commercial-grade hacking tools, methodologies, and techniques required by hackers.
- 40 Hours Instructor led Online Training
- Authorized Digital Learning Materials
- Lifetime Free Content Access
- Flexible Schedule Learn Anytime, Anywhere.
- Training Completion Certificate
- 24x7 After Course Support
Accreditation with